A weak password is one way your computer can be compromised according to computer security experts at Webroot.
I taught computer literacy for nine years. Computer and internet security was one component of that class. I use what I considered strong passwords.
Yet my email account was recently hacked. It was embarrassing and annoying, but at least I was in good company.
Six e-mail accounts belonging to members of the Bush family were recently hacked with some of the contents posted online. For the full account, read here.
After the Bush episode, most computer users recognize that hacking could happen to ALL of us. After personally being hacked, I am more convinced than ever that no one is immune to a hacker.
If you have weak passwords, you are at even higher risk. I offer these tips to making your password stronger.
- AVOID dictionary words.
Password cracking programs contain a dictionary filled with commonly used dictionary words which means your Harriedme201 is crackable in mere seconds.
- AVOID names.
All of us like to use pet names, favorite book characters, actors or actresses names, or names of places we’ve been. Hackers always look for these. Again easily crackable.
- AVOID using any part of your email account as a password.
This is a hard one to follow because, as professional writers, we all want name recognition. What better way than using our name at our namewebsite.com as our email address. Experts tell us we are asking for trouble without a strong password.
Wt4e-79P-B13^qS is an example of a strong password. So how do you create a STRONG password?
- USE a minimum of 10 characters in your password. Best are passwords with more than 15 characters. Why? The more letters the harder to crack.
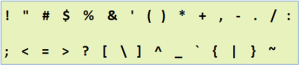
- USE uppercase, lower case letter, numbers, and special characters randomly throughout your password. Be creative. Don’t substitute obvious symbols for obvious letters, i.e. 1 or ! for the letter L, @ for A, etc.
Here’s a chart of useable special characters acceptable for password use.
You can also use emoticons smiley faces such as these to create a strong password:
For more ways to change your weak password, check out this site.
Once you have your strong password, follow these suggestions:
- USE a unique password for each site you visit. It’s a daunting task-creating and memorizing multiple passwords. However, it is the smartest way to avoid being hacked.
- CHANGE your password at least twice a year. Better: change it every 45 to 90 days.
- GUARD your passwords. You can use password programs or create your own method, but decide how you’re going to keep up with your passwords and begin keeping track.
Edie Melson has some excellent ideas for safeguarding your passwords. Check out her blog here.
Will using a strong passward prevent hacking of your accounts? Maybe, maybe not, but following these tips can’t hurt.
YOUR TURN: Are you using a weak password?


[…] Do you use weak passwords on-line? (judythewriter.wordpress.com) […]
[…] For tips and suggestions on how to do this, read the first part of this series here. […]
[…] Do you use weak passwords on-line? (judythewriter.wordpress.com) […]
Great article, easy to follow and a very important topic!!
Thanks. Glad you enjoyed the article and hope you stop by the front porch again.
[…] Do you use weak passwords on-line? (judythewriter.wordpress.com) […]
First off I have to say I love the variety of your posts! Then I’ll add that I started changing all my passwords at the end of 2012..using the variety of numbers I always get as confirmation numbers for online bill paying. Just mixing numbers and letters and adding a dash of punctuation marks now and then. BUT a body has to write those new passwords down as they aren’t the standard run-of-the-mill kind. Janie C
Yep. The big issue with those secure passwords and different passwords is keeping up with them. I have a system, but I still worry about security. Thanks for stopping by and sharing,
Guilty!
Aren’t we all? That’s why I wrote the post so we could “fix” things. LOL
Judythe, this information is sooooooo critical! Thank you for sharing your expertise.
Thanks, Edie. And thanks for your blog that offers even better expertise for this wild world of social media and on-line living.